Our Technology Services
We provide a variety of different solutions within the technology space. Anything from cyber security to networks and telephony.
Cyber security is at the heart of everything we do. We always focus on delivering solutions that are as secure as possible. These solutions include email security, end point protection, password security, DMARC management, firewalls etc.
Our network planning and design experts, provide comprehensive solutions for every stage of network implementation, from LAN and WAN design to network troubleshooting and support.
With our network engineering services, you can ensure your network architecture design is optimised for performance and security, while also taking advantage of cloud network management.
Wireless Surveys
We have access to some of the best wireless survey and design engineers in the UK. We use the latest tools and technology and combined with over 30 years of experience, we ensure that you get the best possible wireless solution.
Reliable wireless solutions start with a proper wireless survey.
The type of survey required depends on the goals and circumstances of the wireless network deployment. Conducting the appropriate survey helps optimise network performance, ensure coverage and signal quality, identify and mitigate interference, and meet the specific requirements of the wireless network environment.
For wireless surveys we use a mixture of Hamina, Ekahau and Tamograph depending on the type of survey and environment that is being surveyed.
Support Services
All of our services can be provided on the same monthly or one off invoice.
Cyber Security
Our solutions and services are
- EDR/MDR endpoint protection
- Password protection
- Email security
- Content filtering
- Managed firewall services
- Compliance reports
- SOC/SIEM solutions

IT Support
We cover network devices laptops, tablets and mobile devices via our own team and we outsource server support to a partner. We provide licenses and hardware as well as remote and onsite support.
Complementary Services
We excel in the service listed about but that’s just the beginning of what we offer.
Our wide range of services are designed to ensure a seamless wired and wireless network solution from start to finish.
We pride ourselves on delivering a customised approach tailored to your unique requirements.

Internet Connectivity
Internet connectivity – We have access to circuits from almost every provider in the UK. If you provide us with your requirements and your address, then we will select the best options for you.
We provide the following connectivity options:
- Fibre broadband
- Leased lines
- Satellite
- Last mile wireless

Data Cabling
Data Cabling – Most businesses have a mixture of wired and wireless networks and wireless access points should use wired backhaul where possible.
Our team will take care of any of your data cabling needs.
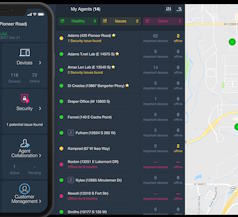
Maintenance and Managed Services
There is no point in paying for a great solution if you don’t maintain it. Our expert team will monitor the solution, as well as recommending and implement preventative maintenance to maximise your up time.
Our network management solutions provide end-to-end support for your network needs, including monitoring and management, scalability and expansion, and network integration services. Trust us to help your business achieve peak network performance and efficiency with our proven network optimisation strategies.

Consultancy and Resource
Do you need expertise but can’t justify hiring someone full time? Then our consulting services can help.
We can provide you with consultancy services on an hourly, daily or monthly basis.
We can provide the following resources:
- CIO/CTO as a service
- CISO as a service
- Wireless survey engineer
- Wireless troubleshooting and consultancy
- Network architect
- Firewall consultant
- WiFi, network or firewall installation engineers

Telephony
Our Cloud based Telephony platform has lots of features eg
- Call logging
- Call recording
- Call forwarding
- Messaging
- Call stats dashboard
- Front end IVR
- Call Queueing
- And many more
If you’re looking for a partner for all of your IT needs, then trust in Castra Solutions and we will be by your side every step of the way.
Our team is here to cater to all your IT needs, drawing from our vast experience and reliable partner services.
Reach out to us today and let us guide you through a seamless technology experience tailored just for you.

